🔥 Subscribe to Our Monthly Security Digest Newsletter
Specific, actionable requirements that outline what needs to be implemented to protect software from potential threats, vulnerabilities, and risks.
SECURE DEVELOPMENT CHALLENGES
When software security is treated as an afterthought, rather than a vital step in the development process, it can lead to vulnerabilities in production, putting customer data at risk.
Manually gathering security requirements and addressing weaknesses can take weeks to
months.
Manual security tasks increase vulnerability risks in production, causing breaches and compliance issues, which erode customer trust.
Slow, unscalable security methods delay software launch, harming competitiveness and reducing revenue for organizations.

Based on the attributes of the project/
software (e.g., programming languages, architectures, etc.)
Based on the attributes of the project/software (e.g., programming languages, architectures, etc.)

Align generated requirements to industry standards like OWASP ASVS, PCI DSS, ISO
27001, NIST 800-5



Automate the generation and delivery of requirements for a large number of applications or projects, ensuring consistency across the organization
Automate the generation and delivery of requirements for a large number of applications or projects, ensuring consistency across the organization

Maintain traceability of security requirements to ensure alignment with security policies and regulatory frameworks
Maintain traceability of security requirements to ensure alignment with security policies and regulatory frameworks
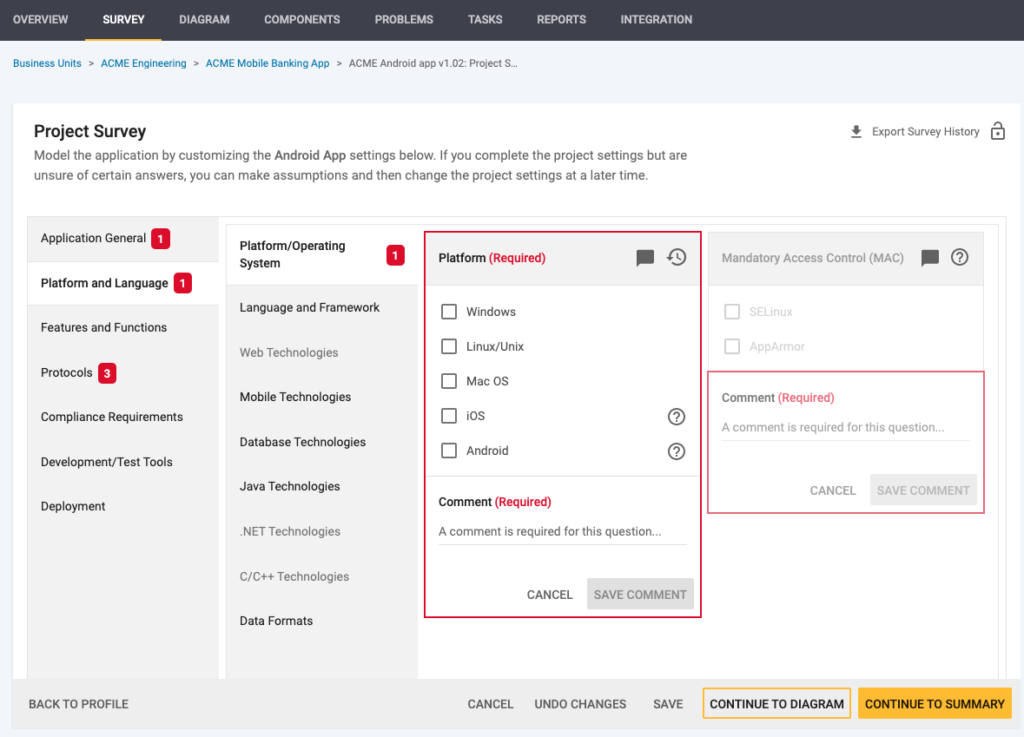
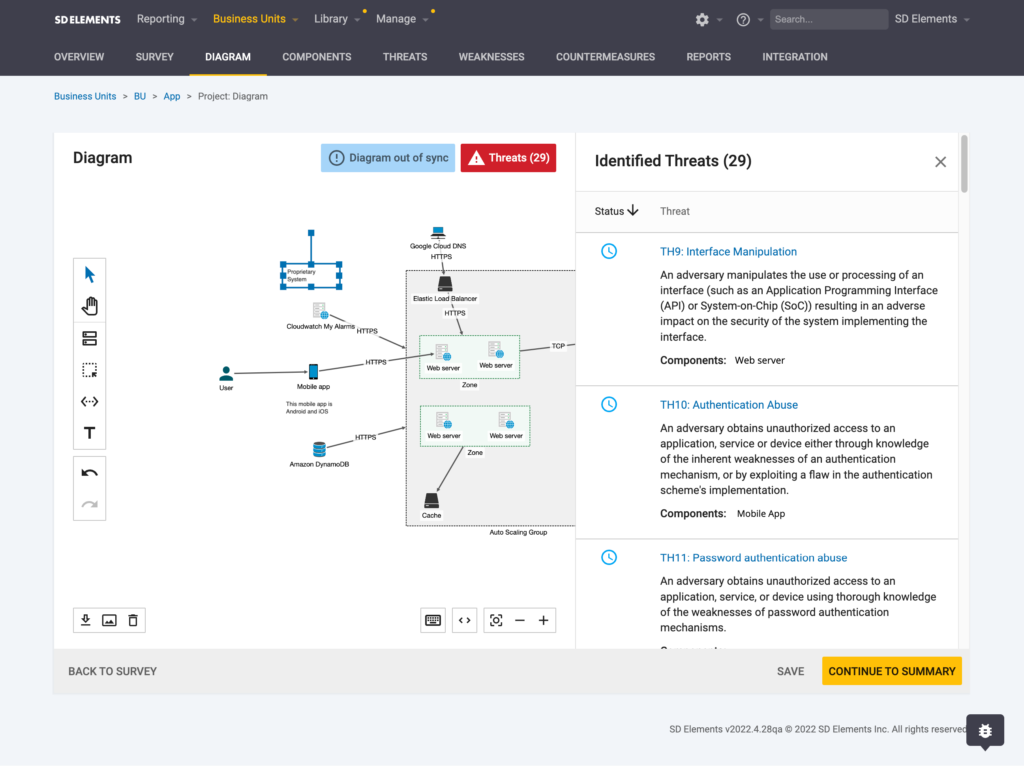
Gather system context from architecture diagrams, repositories, developer tools, or structured inputs to understand your project’s technology stack and functionality.
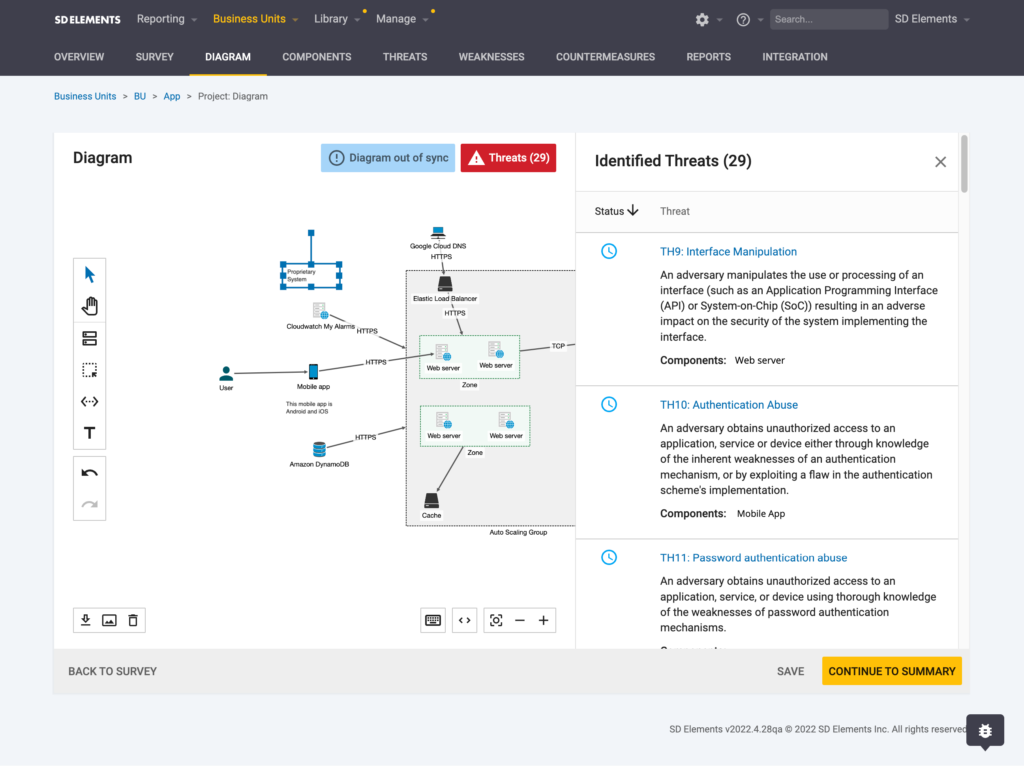
SD Elements gathers and identifies the proper security, privacy, and compliance requirements in a matter of seconds
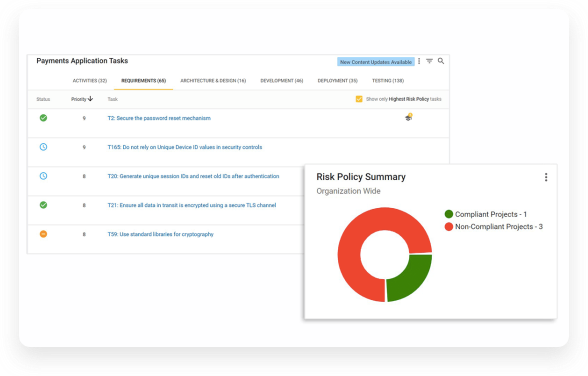
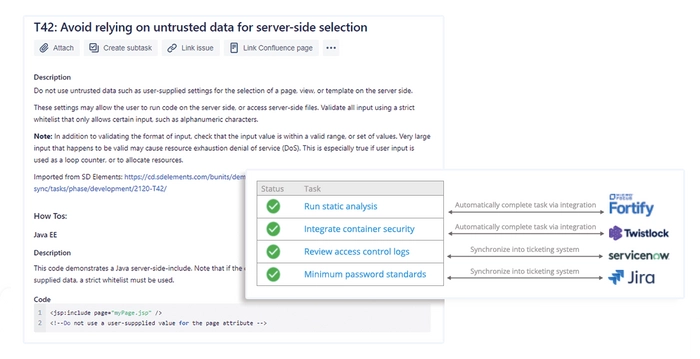
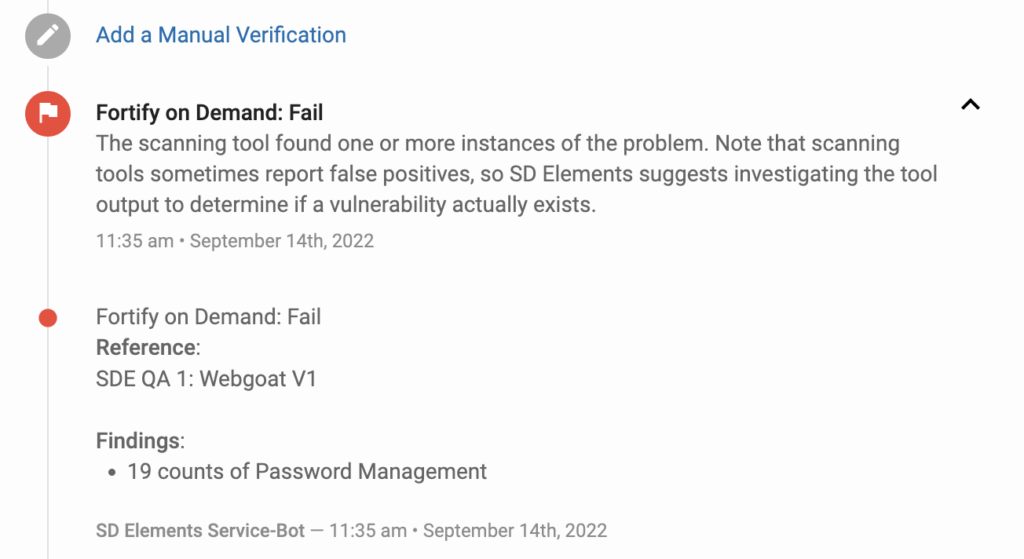
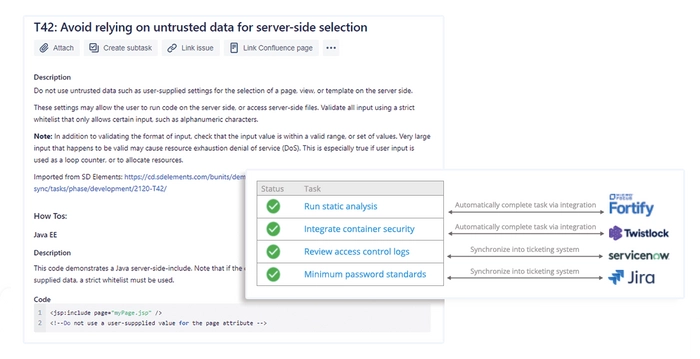
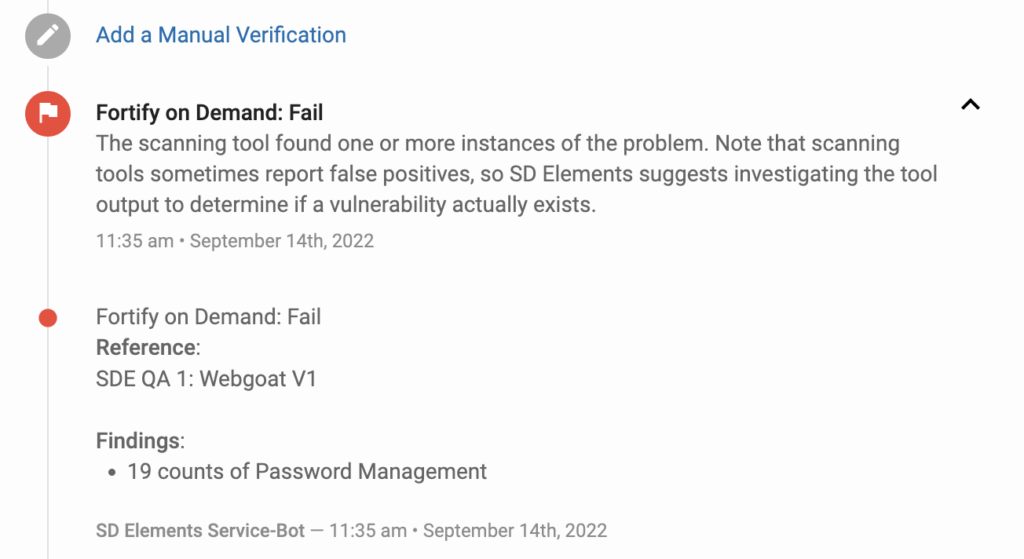
SD Elements delivers prescriptive security controls aligned with each security requirement.
SD Elements offers bite-sized training modules to provide developers with best practices in how to complete their security tasks
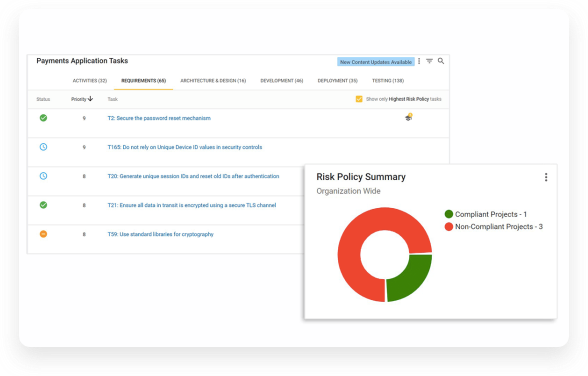
SD Elements provides visibility into the security and compliance state of your software across your entire software portfolio (including open source software and components purchased from third party providers) by using near-real time reporting
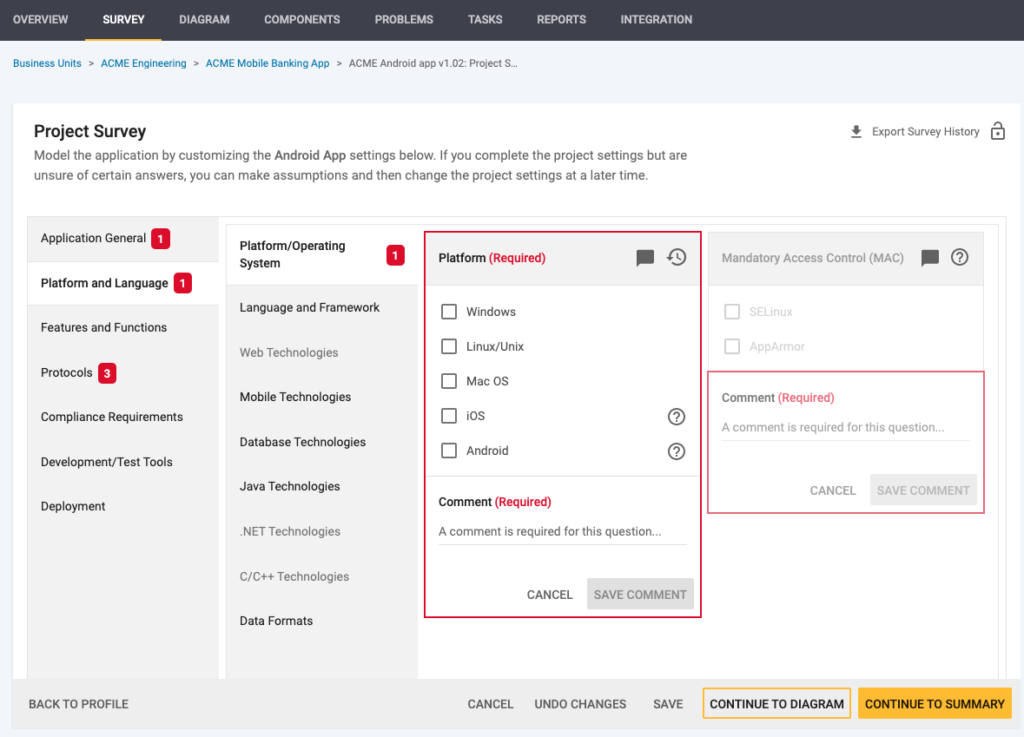
Gather system context from architecture diagrams, repositories, developer tools, or structured inputs to understand your project’s technology stack and functionality.
SD Elements gathers and identifies the proper security, privacy, and compliance requirements in a matter of seconds
SD Elements delivers prescriptive security controls aligned with each security requirement.
SD Elements offers bite-sized training modules to provide developers with best practices in how to complete their security tasks
SD Elements provides visibility into the security and compliance state of your software across your entire software portfolio (including open source software and components purchased from third party providers) by using near-real time reporting



Product Security Governance, Architecture & Risk Management,
Johnson Controls



Director of Cyber & Information Security, FINRA



Vice President and CISO,
Cubic
Get answers to common questions about defining, managing, and scaling security requirements in modern software development.
Security requirements define what needs to be implemented, while security controls define how those requirements are enforced. Together, they ensure that applications meet security standards and reduce risk.
Set up a meeting with one of our security experts to see a demo of SD Elements